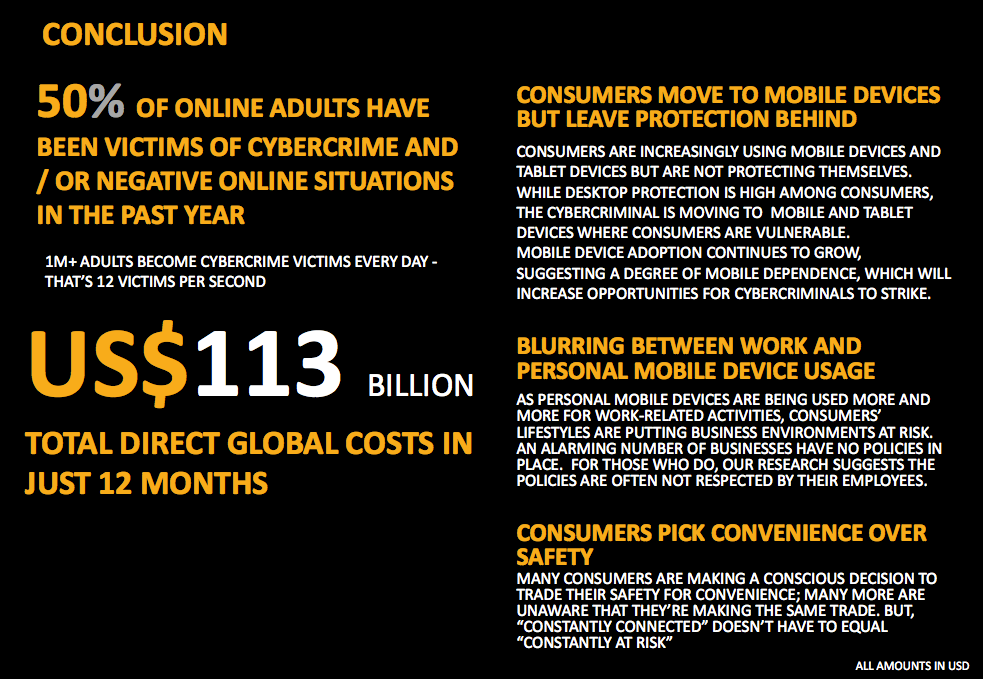
The Norton 2013 Cybercrime Report provided a good basis to propose an initiative for the 2014 strategic plan. The HR in me would not want to pass this opportunity to be proactive and take on a lead role in reducing the risk exposure of the company and its employees to cybercrime. This will be the topic of this article, the 3rd instalment of my 3 post-mini-blog series about the 2013 Norton Report. To start the ball rolling, let’s have a brief review:
- We started this mini-series with a post about the highlights of the Norton Report where online behaviour and the cost of cybercrime takes centre stage.
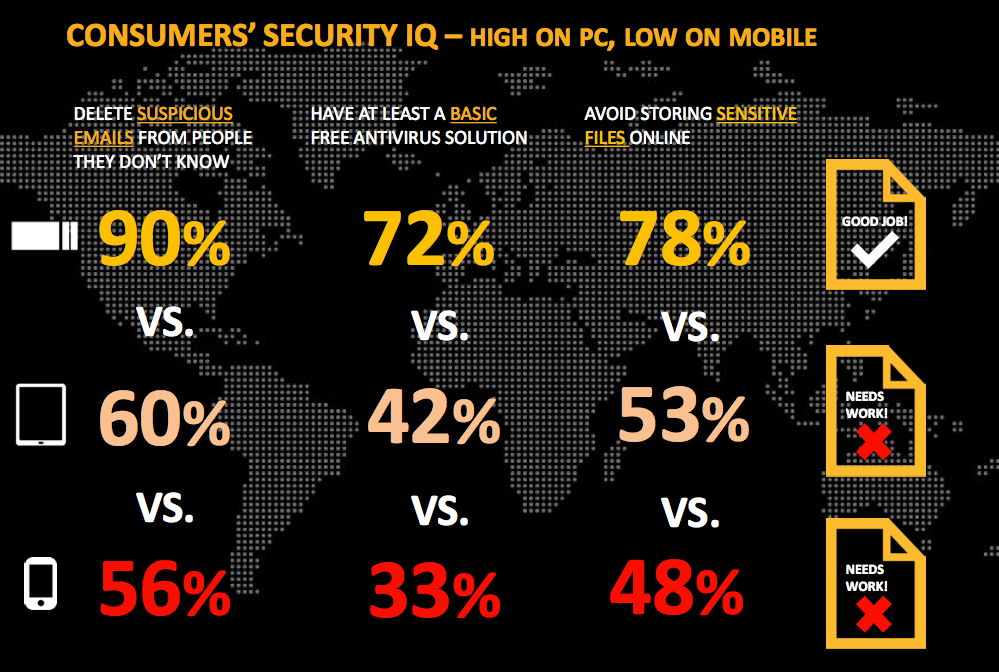
- With the growing mobile device users and cheap data access, I focused my 2nd article on mobile cybercrime and the need for mobile device safety awareness campaign.
Now to lay down the basis for the HR initiative, let’s go back to Norton’s findings:
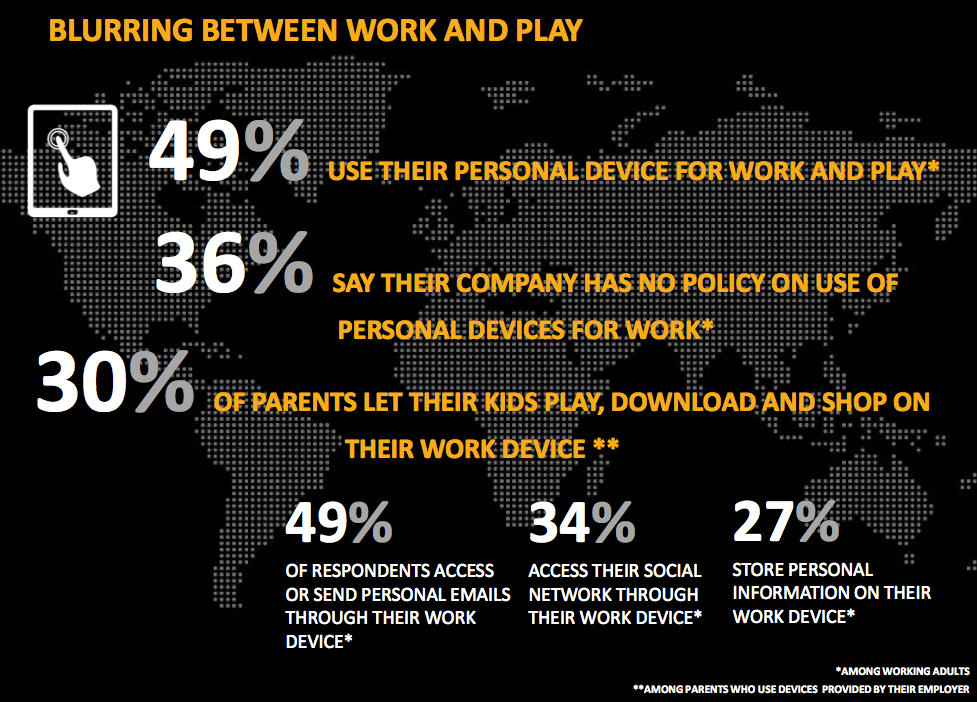
Though only key positions are given company-issued mobile devices (laptop, tablets, smartphones), these employees are likely to access confidential and proprietary information using their mobile devices, and in some cases, store this info on their device. In the absence of safety and security guidelines, the company may be at risk.
Likewise, the absence of clear-cut guidelines or culture of liberality on the use of company-issued devices may put at risk mobile devices from malware, and find their way to the company network.
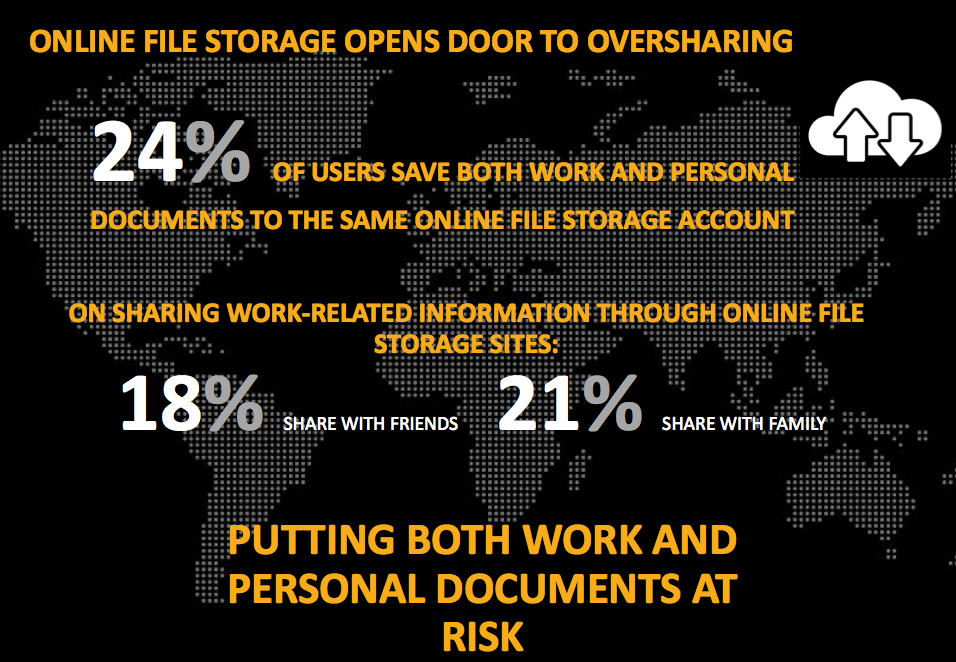
When USB ports are disabled on most company computers, employees resort to cloud storage or social networks to save and access their files in real-time to continue working at home or off-site.
Now, this is where the strategic function of HR comes in handy. Since the online security gap is about employee behaviour and can be addressed by guidelines, policies and orientation/training, HR should initiate and take the lead in providing a solution.
In my observation, this is the main reason why a company, through its employees, can be at risk of cybercrime.
Without online philosophy, digital and mobile safety guidelines & policies, and employee training, behaviour of employees can place the company at risk.
As a Brand, Social Business and HR/OD Strategist rolled in one as a consequence of my organic work in HR/OD, early adoption to Social Web and hands-on experience to digital marketing, here’s my recommendation:
We can find the balance between liberality & creativity on one end (fun side), and security and control on the other (boring side).
As strategic partner, HR should collaborate with IT, Marketing and Corporate Communications (if this function is not part of either HR or Marketing) to draft an all-inclusive online philosophy, digital and communication strategy, social web and mobile safety guidelines & policies. The group’s output can be used as the basis for employee orientation and training on “mobile and surf safe habits“, “online reputation management” and “personal and corporate privacy”. IT can propose anti-virus solutions and other interventions to protect the company network and IT infrastructure, while Marketing can provide the framework for brand management and Corp. Communications, the framework on social media and online postings and communications.
Below are the consequences of a lack of digital framework and social web guidelines/policies if an initiative fails to take off.
- Employer branding is not aligned to marketing’s overall brand strategy
- Employees will use social media, unofficially, to get work done, i.e. unofficial creating a fan page for recruitment
- Employees will use social media to rant displeasure to their boss or organisation.
- The employee will over share- confidential, proprietary and strategic information being shared by loyal, proud and over-enthusiastic employee
- There will be unregulated and unsecured use of cloud storage
- There will be undefined and blur lines between fun and work
- Unclear responsibility of recipients of company-issued mobile devices
- Employee misuse of marketing collaterals on social media
These undoubtedly will result to
- Employer reputation being tarnished by employee online behaviour
- Loss of strategic advantage when confidential and propriety information is accidentally leaked-out
- Compromised mobile devices, and eventually the company network
- Waste of company time and resources
- for uncoordinated and unaligned strategies
- man-hours lost for unregulated use of internet and social web of employees
- bandwidth wastage for unregulated use of internet and social web of employees
Corporate inaction to harness opportunities and prevent the risk provided by mobile and social computing will result in substantial losses in real money, strategic advantage and other resources.
Speak up and let me know your thoughts.
Discover more from ASKSonnie.INFO
Subscribe to get the latest posts sent to your email.